I had shortly a customer question how his non-global admin user could see non-owner mailbox access’. Focus on the following words: NON-global admin & non-owner mailboxes. You will see later on this post why these facts are so important.
As I just answered him, ‘for sure, not a big deal. I can show you right now‘:
I had to realised it won’t be so easy.
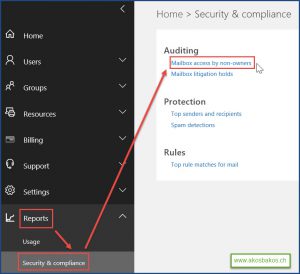
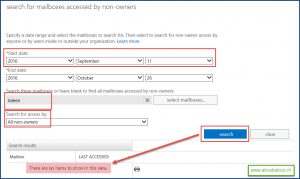
Neither in Office 365 Portal in Security & Compliance part nor in Exchange Admin Center, these reports couldn’t have any result. They were everywhere empty:
After some Microsoft discussions (thank for helping me again Oana & Gabriel) we found together the following complex solution for my customer.
First part of this request:
- Connect to Exchange Online via PowerShell
Set-Executionpolicy unrestricted $LiveCred = Get-Credential $Session = New-PSSession -ConfigurationName Microsoft.Exchange -ConnectionUri https://outlook.office365.com/powershell-liveid/ -Credential $LiveCred -Authentication Basic -AllowRedirection Import-PSSession $Session -Allowclobber Connect-MsolService -Credential $LiveCred
In case you are not familiar with PowerShell –> change your IT job! Bad joke… 🙂
PowerShell can be downloaded from here: https://msdn.microsoft.com/en-us/library/jj151815.aspxScroll down until you reach Install Azure AD Module.– First install the Microsoft Online Services Sign-In Assistant for IT Professionals RTW from the Microsoft Download Center.– Then install the Azure Active Directory Module for Windows PowerShell (64-bit version), and click Run to run the installer package.After it is successfully installed, right click on it and Run As an administrator. - Default is auditing for mailboxes is not enabled.
To enable mailbox auditing run the following command:Get-Mailbox -ResultSize Unlimited -Filter {RecipientTypeDetails -eq "UserMailbox"} | Set-Mailbox -AuditEnabled $true - By design this owner audit action is not enabled as well.
 To enable all actions on delegate access, use this command:
To enable all actions on delegate access, use this command:
Get-Mailbox -ResultSize Unlimited -Filter {RecipientTypeDetails -eq "UserMailbox"} | Set-Mailbox -AuditEnabled $true -AuditDelegate FolderBind, Create, HardDelete, Move, MoveToDeletedItems, SendAs, SendOnBehalf, SoftDelete, UpdateFor my issue, the FolderBind action wasn’t allowed by default. This action is for mailbox access report. It is also logged when the admin or delegate opens the mailbox. More information about mailbox auditing, keep the following Technet article close: https://technet.microsoft.com/en-us/library/dn879651.aspx
Important: entries for folder bind actions performed by delegates are consolidated. One log entry is generated for individual folder access within a time span of 24 hours.
After these steps, global admins are allowed to see this report either in Office 365 Portal in Security & Compliance part respectively Exchange Admin Center or by PowerShell:
Search-MailboxAuditLog -StartDate '2016-xx-xx'-EndDate '2016-xx-xx' -LogonTypes @('admin','Delegate') -ExternalAccess:$false -identity 'MBX' -showDetails:$true -resultSize 501
Second part of this request: Azure Active Directory users without global admin rights want to see this report as well. Regarding these two official Microsoft articles ‘give users access to auditing reports‘ and ‘search the audit log in the Office 365 Security & Compliance Center‘, it should work, right? No, it doesn’t.
I show you hereby how easily it can be solved:
- Create a new Exchange admin role in the EAC with view-only audit logs role
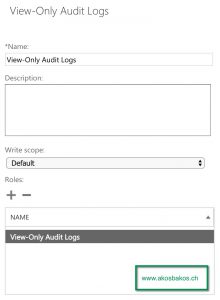
- Assign your non-admin users to this role.
- Following link can be communicate to the end users: https://outlook.office365.com/ecp/Reporting/NonOwnerAccessReport.aspx
They are just simplify able to open it after AAD login. - For better user experience and customer satisfaction, I just published as a simply web application link into the myapps.microsoft.com portal

I hope these solutions respectively workaround can help you and your customer to open this Exchange Online auditing reports for non-owner mailboxes.

Permalink
Great article, very well structured! I am sure it will be useful for many administrators into guiding their end users into such reports, and also for the admins themselves.
Keep up the good work and thanks for sharing this with us! 🙂
Permalink
Oana, thanks for your nice words.
And thanks again for working together to solve my issue.